How to Update your EHCP force Version.
Posted: Wed Jan 17, 2018 5:14 pm
IMPORTANT INFORMATION:
Never under any circumstances, run the EHCP force update script from the official EHCP force website, as it may DESTROY YOUR INSTALLATION.
Running the official EHCP force update script may result in the need to do a FULL SERVER REINSTALL.
To update EHCP force you MUST use the update script from within this post.
Most EHCP force updates (but not all) are NOT WORTH THE RISK.
My update script first backs up all the critical files that may be overwritten by the update, it then runs the official update routine, then it restores the critical files, finally it reboots your server.
Each time an EHCP force update is released, you must wait until I have tested it, as some updates may cause issues despite my script, once I have tested it, I will publish it on this page.
I may change the update script to make future updates safe, so you should always download the latest version of my script, each time you perform an update.
When an EHCP force update comes out, you should wait until this post is updated with the details of the new update. So, if the information on this site does not match what is on the EHCP force site, do not perform the update.
Here is the link to check the EHCP force website:
https://ehcpforce.ezpz.cc/forums/index.php?topic=15.0
The current situation regarding EHCP force updates is not ideal.
--LATEST UPDATE INFORMATION--
LATEST EHCP force Update: 25 March 2026
GAIN FROM UPDATE: Very Low.
UPDATE STATUS: Not Required.
MORE INFO:
This update is already incorporated into the first Ubuntu 26.04 modified version of EHCP force on this site.
ALL EHCP force updates pose a small risk but significant risk to your server.
When you are 100% sure you want to take the risk, please read on.
HOW TO PERFORM AN UPDATE:
Login to your server using your PC and PuTTY.
Issue this command to download the latest update script.
wget https://downloads.ghostnetwork.co.uk/scripts/ehcpforce/2604/updateehcp.sh -O updateehcp.sh
Give the script permission to execute using this command.
sudo chmod +x updateehcp.sh
Next, run the script using this command.
sudo bash updateehcp.sh

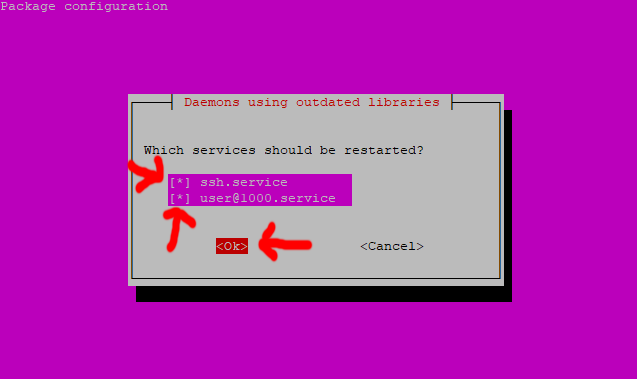
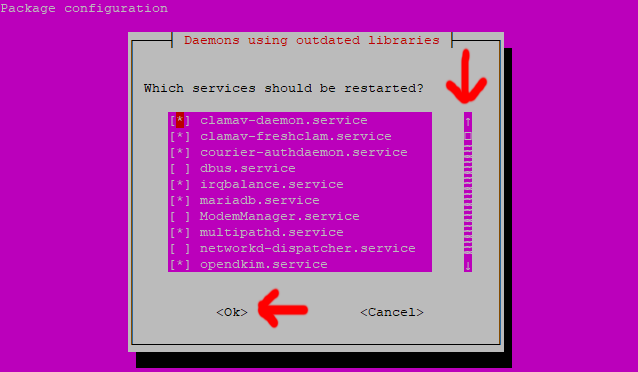
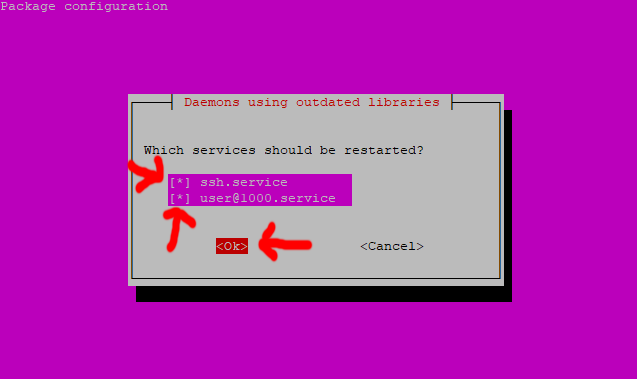
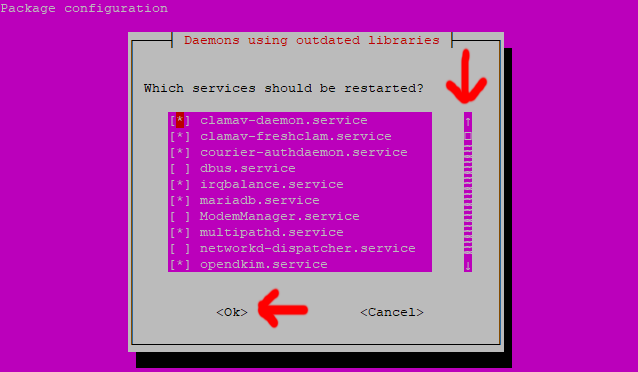
As per always with EHCP, ignore any errors you see scrolling past.
When the script has finished, you will be asked to press any key to reboot, so please do so.
Finally, when your server has fully rebooted, you should log back in using PuTTY.
Issue this command to delete the script (so an outdated version is not accidentally run).
sudo rm updateehcp.sh
You can now log out of PuTTY, using the exit command.
We are done here.
FOR INFORMATION PURPOSES ONLY:
This is the code within the latest update script.
Never under any circumstances, run the EHCP force update script from the official EHCP force website, as it may DESTROY YOUR INSTALLATION.
Running the official EHCP force update script may result in the need to do a FULL SERVER REINSTALL.
To update EHCP force you MUST use the update script from within this post.
Most EHCP force updates (but not all) are NOT WORTH THE RISK.
My update script first backs up all the critical files that may be overwritten by the update, it then runs the official update routine, then it restores the critical files, finally it reboots your server.
Each time an EHCP force update is released, you must wait until I have tested it, as some updates may cause issues despite my script, once I have tested it, I will publish it on this page.
I may change the update script to make future updates safe, so you should always download the latest version of my script, each time you perform an update.
When an EHCP force update comes out, you should wait until this post is updated with the details of the new update. So, if the information on this site does not match what is on the EHCP force site, do not perform the update.
Here is the link to check the EHCP force website:
https://ehcpforce.ezpz.cc/forums/index.php?topic=15.0
The current situation regarding EHCP force updates is not ideal.
--LATEST UPDATE INFORMATION--
LATEST EHCP force Update: 25 March 2026
GAIN FROM UPDATE: Very Low.
UPDATE STATUS: Not Required.
MORE INFO:
This update is already incorporated into the first Ubuntu 26.04 modified version of EHCP force on this site.
ALL EHCP force updates pose a small risk but significant risk to your server.
When you are 100% sure you want to take the risk, please read on.
HOW TO PERFORM AN UPDATE:
Login to your server using your PC and PuTTY.
Issue this command to download the latest update script.
wget https://downloads.ghostnetwork.co.uk/scripts/ehcpforce/2604/updateehcp.sh -O updateehcp.sh
Give the script permission to execute using this command.
sudo chmod +x updateehcp.sh
Next, run the script using this command.
sudo bash updateehcp.sh

As per always with EHCP, ignore any errors you see scrolling past.
When the script has finished, you will be asked to press any key to reboot, so please do so.
Finally, when your server has fully rebooted, you should log back in using PuTTY.
Issue this command to delete the script (so an outdated version is not accidentally run).
sudo rm updateehcp.sh
You can now log out of PuTTY, using the exit command.
We are done here.
FOR INFORMATION PURPOSES ONLY:
This is the code within the latest update script.
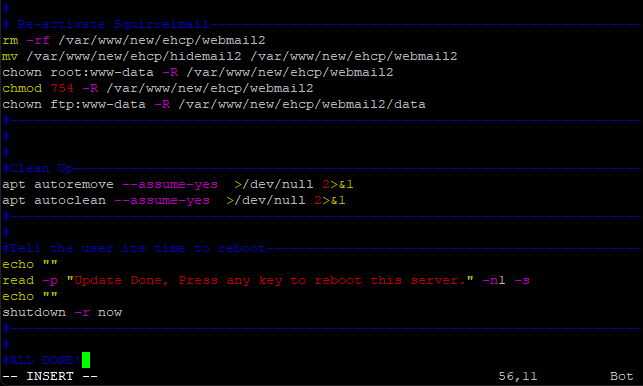
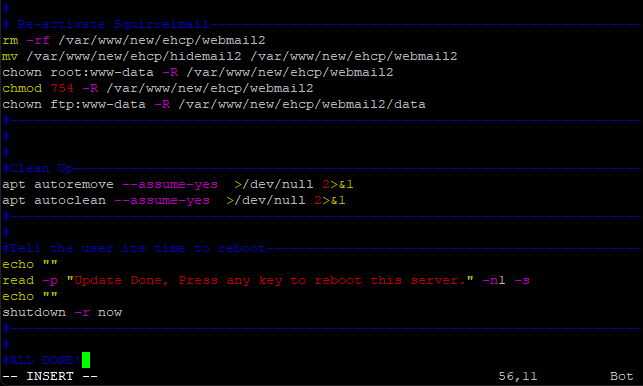
Code: Select all
#!/bin/bash
#
# EHCP force update script by Rob Swan (WA) V.2.12
#
#Check for root-----------------------------------------------------------------
ROOTUID="0"
if [ "$(id -u)" -ne "$ROOTUID" ] ; then
echo "This script must be executed with root privileges."
exit 1
fi
# Check for Ubuntu updates ----------------------------------------------------
apt-get update
apt-get upgrade --assume-yes
apt-get dist-upgrade --assume-yes
#-------------------------------------------------------------------------------
#
# Protect the Squirrelmail installation ---------------------------------------
mv /var/www/new/ehcp/webmail2 /var/www/new/ehcp/hidemail2
#-------------------------------------------------------------------------------
#
# Protect the Install.lib ------------------------------------------------------
cp /var/www/new/ehcp/install_lib.php /var/www/new/ehcp/install_lib.hide
#-------------------------------------------------------------------------------
#
# Protect pam_dbauth_smtp.py ---------------------------------------------------
cp /etc/security/pam_dbauth_smtp.py /etc/security/pam_dbauth_smtp.hide
#-------------------------------------------------------------------------------
#
# I have trust issues, protect the saslauthd config (if installed)
if test -f /etc/pam.d/smtp; then cp /etc/pam.d/smtp /etc/pam.d/smtp.hide; fi
if test -f /etc/default/saslauthd; then cp /etc/default/saslauthd /etc/default/saslauthd.hide; fi
if test -f /etc/postfix/sasl/smtpd.conf; then cp /etc/postfix/sasl/smtpd.conf /etc/postfix/sasl/smtpd.hide; fi
if test -f /usr/lib/systemd/system/saslauthd.service; then cp /usr/lib/systemd/system/saslauthd.service /usr/lib/systemd/system/saslauthd.hide; fi
#------------------------------------------------------------------------------
#
# Run the EHCP force update----------------------------------------------------
cwd=$(pwd)
mkdir -p ~/Downloads
sudo apt-get -y install git
cd ~/Downloads
if [ -e "ehcp" ]; then
rm -rf "ehcp"
fi
git clone "https://github.com/earnolmartin/EHCP-Force-Edition.git" "ehcp"
cd ehcp
cd ehcp
bash "ehcpforceupdate.sh" "update"
cd $cwd
#-------------------------------------------------------------------------------
#
# Re-activate Squirrelmail------------------------------------------------------
rm -rf /var/www/new/ehcp/webmail2
mv /var/www/new/ehcp/hidemail2 /var/www/new/ehcp/webmail2
chown root:www-data -R /var/www/new/ehcp/webmail2
chmod 754 -R /var/www/new/ehcp/webmail2
chown ftp:www-data -R /var/www/new/ehcp/webmail2/data
#-------------------------------------------------------------------------------
#
# Restore install.lib-----------------------------------------------------------
mv /var/www/new/ehcp/install_lib.hide /var/www/new/ehcp/install_lib.php
#-------------------------------------------------------------------------------
#
# Restore saslauthd (if installed)
service saslauthd stop
if test -f /etc/default/saslauthd.hide; then mv /etc/default/saslauthd.hide /etc/default/saslauthd; fi
if test -f /etc/postfix/sasl/smtpd.hide; then mv /etc/postfix/sasl/smtpd.hide /etc/postfix/sasl/smtpd.conf; fi
if test -f /usr/lib/systemd/system/saslauthd.hide; then mv /usr/lib/systemd/system/saslauthd.hide /usr/lib/systemd/system/saslauthd.service; fi
systemctl daemon-reload
if test -f /usr/lib/systemd/system/saslauthd.service; then service saslauthd start; fi
#-------------------------------------------------------------------------------
#
# Restore pam_dbauth_smtp.py ---------------------------------------------------
cp /etc/security/pam_dbauth_smtp.hide /etc/security/pam_dbauth_smtp.py
#-------------------------------------------------------------------------------
#
# Crontab Fix-------------------------------------------------------------------
crontab -l > mycronfix
sed -i '/#EHCP Force Default Cronjobs/d;1i\#EHCP Force Default Cronjobs' mycronfix
sed -i '/remove_old_php_tmp_session_files.sh/s/$/ >\/dev\/null 2>&1/' mycronfix
crontab mycronfix
rm mycronfix
#-------------------------------------------------------------------------------
#
# saslauthd Fail Roundcube Sending Fail Safe------------------------------------
sed -i "s/'%u';/'';/g" /etc/roundcube/config.inc.php
sed -i "s/'%p';/'';/g" /etc/roundcube/config.inc.php
#-------------------------------------------------------------------------------
#
# pop-before-smtp check---------------------------------------------------------
if dpkg -s dovecot-core &>/dev/null; then
echo "We don't need pop-before-smtp, Removing it!"
DEBIAN_FRONTEND=noninteractive apt-get remove pop-before-smtp -y
DEBIAN_FRONTEND=noninteractive apt-get purge pop-before-smtp -y
fi
#
#Clean Up-----------------------------------------------------------------------
apt autoremove --assume-yes >/dev/null 2>&1
apt autoclean --assume-yes >/dev/null 2>&1
#-------------------------------------------------------------------------------
#
#Tell the user its time to reboot-----------------------------------------------
echo ""
read -p "Update Done, Press any key to reboot this server." -n1 -s
echo ""
shutdown -r now
#-------------------------------------------------------------------------------
#
#ALL DONE!